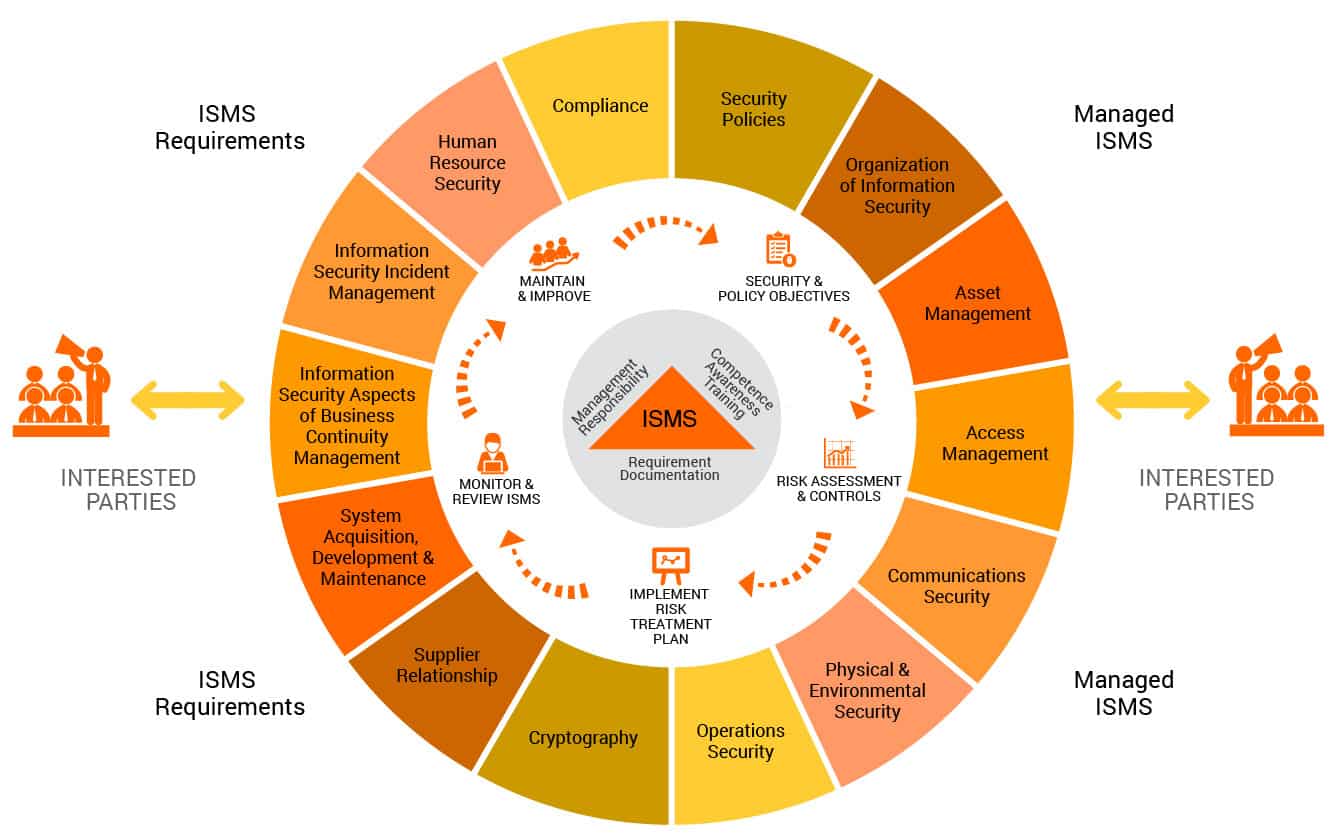
What is the job of Chief Information Security Officer (CISO)
ISMSSince ISO 27001 does not require the CISO, it does not prescribe what this person should do. Generally, this person should coordinate all the activities related to securing the information in a company, and here are some ideas on what this person could do.